
A hybrid espionage/influence campaign conducted by the Russian threat group ‘UNC5812’ has been uncovered, targeting Ukrainian military recruits with Windows and Android malware.
According to Google’s threat intelligence, the campaign impersonated a “Civil Defense” persona along with a website and dedicated Telegram channel to distribute malware through a fake recruitment avoidance app dubbed “Sunspinner” by the researchers.
The campaign targets Windows and Android devices using distinct malware for each platform, giving the attackers data theft and real-time spying capabilities.
Google has implemented protections to block the malicious activity, but the operation highlights Russia’s continued use and extensive capabilities in the cyber-warfare space.
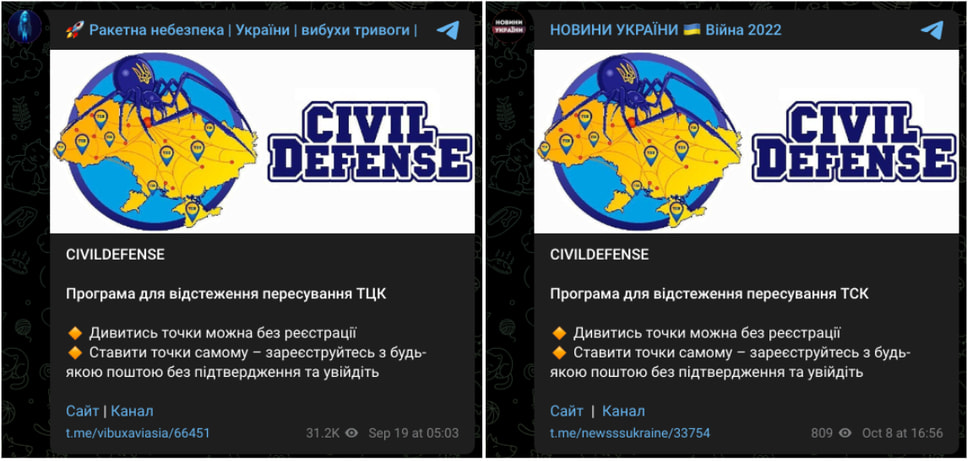
Fake “Civil Defense” persona
UNC5812’s persona does not attempt to impersonate Ukraine’s Civil Defense or any government agencies but is instead promoted as a legitimate Ukraine-friendly organization that provides Ukrainian conscripts with helpful software tools and advice.
The persona uses a Telegram channel and a website to engage potential victims and deliver narratives against Ukraine’s recruitment and mobilization efforts, aiming to stir distrust and resistance among the population.
When Google discovered the campaign on September 18, 2024, the “Civil Defense” channel on Telegram had 80,000 members.
Source: Google
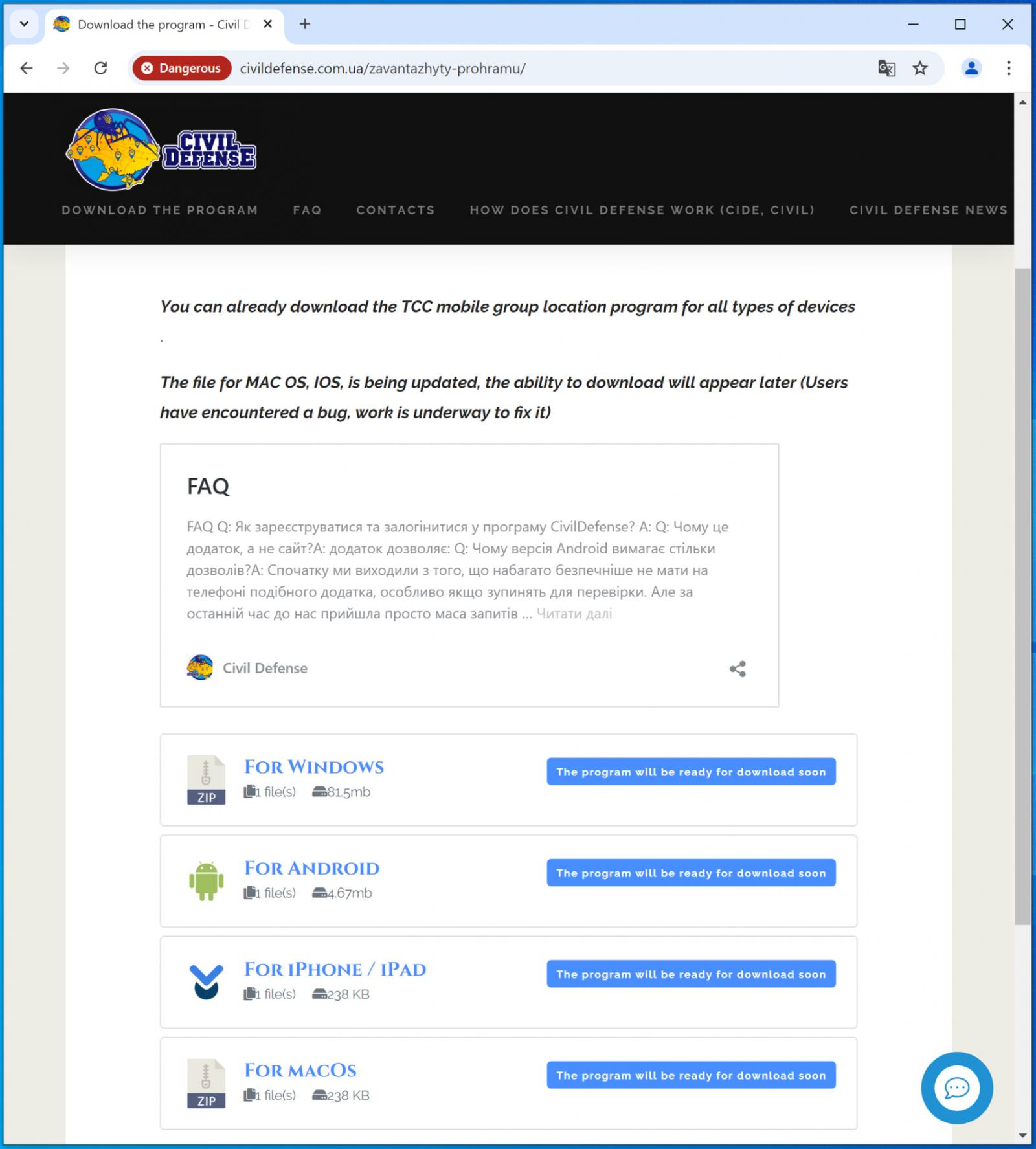
Users tricked into visiting Civil Defense’s website are taken to a download page for a malicious application promoted as a crowd-sourced mapping tool that can help users track the locations of recruiters, and avoid them.
Google calls this app “Sunspinner, and although the app features a map with markers, Google says the data is fabricated. The app’s only purpose is to hide the installation of malware that takes place in the background.
Source: Google
Dropping Windows and Android malware.
The fake apps offers Windows and Android downloads, and promises to add iOS and macOS soon, so Apple platforms are not supported yet.
The Windows download installs Pronsis Loader, a malware loader that fetches additional malicious payloads from UNC5812’s server, including the commodity info-stealer ‘PureStealer.’
PureStealer targets information stored in web browsers, like account passwords, cookies, cryptocurrency wallet details, email clients, and messaging app data.
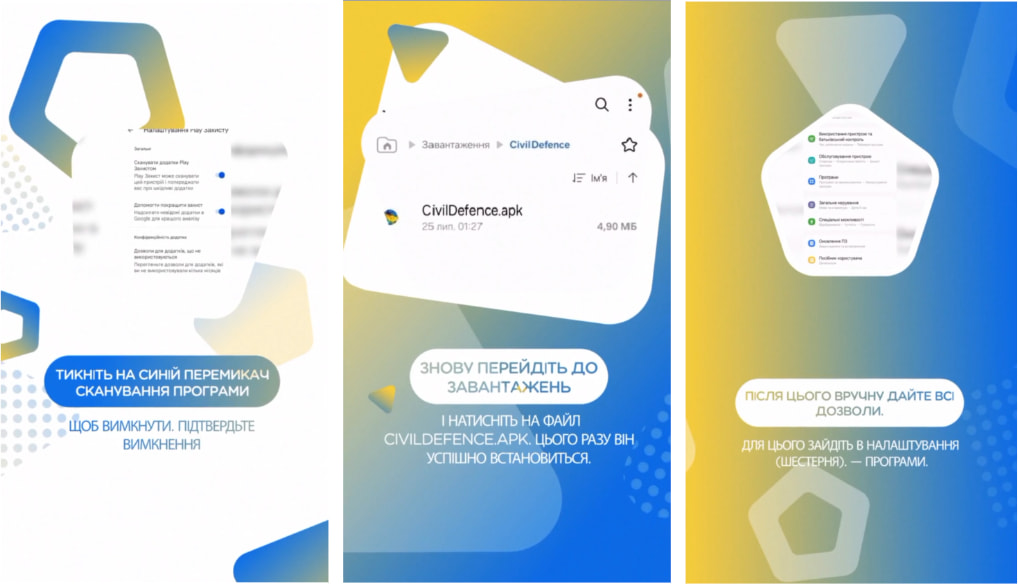
On Android, the downloaded APK file drops CraxsRAT, also a commercially available backdoor.
CraxsRAT allows the attackers to track the victim’s location in real time, log their keystrokes, activate audio recordings, retrieve contact lists, access SMS messages, exfiltrate files, and harvest credentials.
To perform these malicious activities undeterred, the app tricks users into disabling Google Play Protect, Android’s in-built anti-malware tool, and manually grant it risky permissions.
Source: Google
Google updated Google Play protections to detect and block the Android malware early and also added the domains and files associated with the campaign to its ‘Safe Browsing’ feature on Chrome.
The complete list of indicators of compromise associated with the latest UNC5812 campaign is available here.
Note: This article have been indexed to our site. We do not claim legitimacy, ownership or copyright of any of the content above. To see the article at original source Click Here













